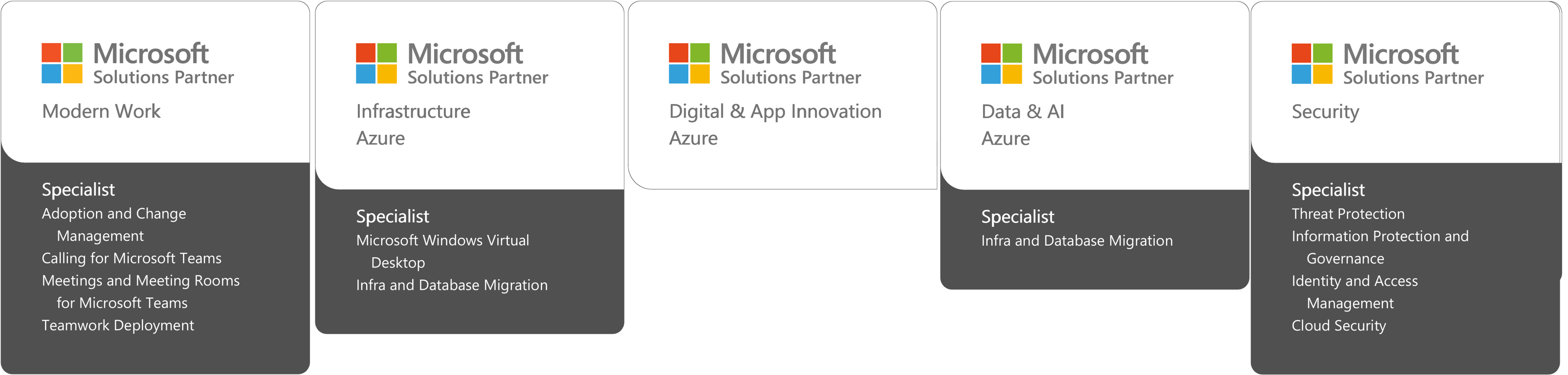
CMMC All In Solution
Built On Microsoft 365 GCC High and Azure Government
%20CMMC%202.0%20Level%202%20Solution%20Set-1.jpg?width=500&height=262&name=(V3)%20CMMC%202.0%20Level%202%20Solution%20Set-1.jpg)
CMMC Level 2 is applicable to organizations supporting the Department of Defense that handle or process the following types of data:
Many, if not most of the DIB and higher education institutions will be required to meet CMMC Level 2.
Implementation of the CMMC Level 2 Solution can include, but is not limited to:
![]() Baselining your Microsoft 365 GCC or GCC High tenant
Baselining your Microsoft 365 GCC or GCC High tenant
![]() Configuring Microsoft Security products to meet NIST 800-171 requirements
Configuring Microsoft Security products to meet NIST 800-171 requirements
![]() Securing corporate devices with Microsoft Intune
Securing corporate devices with Microsoft Intune
![]() Configuring Identity Management and MFA in Azure Active Directory
Configuring Identity Management and MFA in Azure Active Directory
![]() Implementing Microsoft Purview Information Protection (MPIP)
Implementing Microsoft Purview Information Protection (MPIP)
![]() Microsoft Defender for data protection
Microsoft Defender for data protection
Get a Quote
.png)
2 Parade St NW
Huntsville, AL 35806
256.585.6868
info@summit7.us
cmmc@summit7.us
Recent Blog Posts